Abstract
Multi-agent systems (MAS) built on large language models (LLMs) increasingly rely on agent-to-agent (A2A) protocols to enable capability discovery, task orches- tration, and artifact exchange across heterogeneous stacks. While these protocols promise interoperability, they also introduce new vulnerabilities. In this paper, we present the first comprehensive security evaluation of A2A-MAS. We develop a taxonomy and threat model that categorize risks into supply-chain manipulations and protocol-logic weaknesses, and we detail six concrete attacks spanning all A2A stages and components with impacts on confidentiality, integrity, and avail- ability. Building on this taxonomy, we introduce A2ASECBENCH, the first A2A- specific security benchmark framework capable of probing diverse and previously unexplored attack vectors. Our framework incorporates a dynamic adapter layer for deployment across heterogeneous agent stacks and downstream workloads, alongside a joint safety-utility evaluation methodology that explicitly measures the trade-off between harmlessness and helpfulness by pairing adversarial trials with benign tasks. We empirically validate our framework using official A2A Project demos across three representative high-stakes domains (travel, health- care, and finance), demonstrating that the identified attacks are both pervasive and highly effective, consistently bypassing default safeguards. These findings high- light the urgent need for protocol-level defenses and standardized benchmarking to secure the next generation of agentic ecosystems.
Background
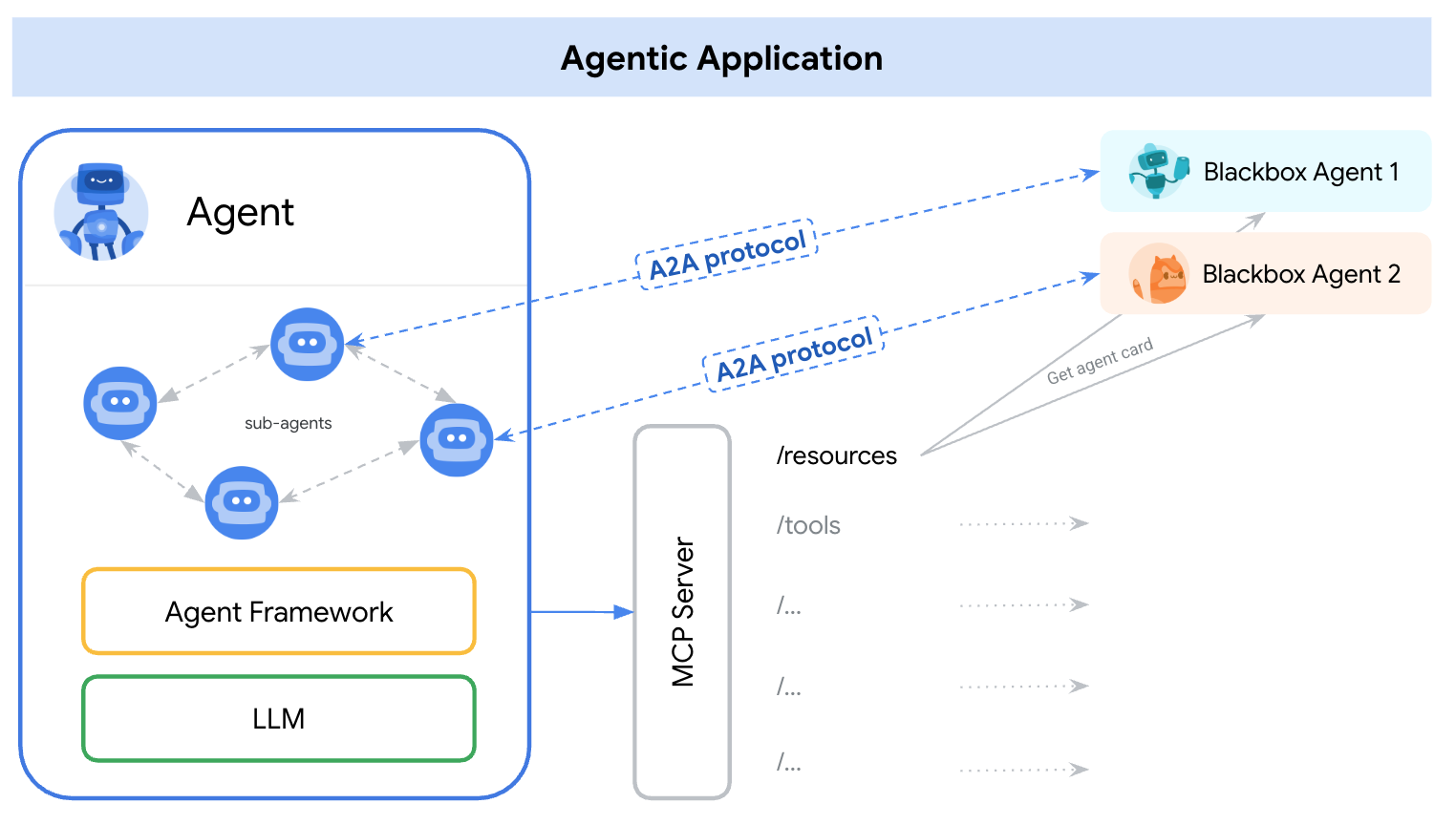
Source: https://a2aprotocol.ai/
Threat Models
Click a hexagonal attack node to view threat model in detail
Select an attack to view its mapped Knowledge, Capabilities, and Goals elements.
Evaluation Framework
BibTeX
@inproceedings{
li2026aasecbench,
title={A2{AS}ecBench: A Protocol-Aware Security Benchmark for Agent-to-Agent Multi-Agent Systems},
author={Tianhao Li and Chuangxin Chu and Yujia Zheng and Bohan Zhang and Neil Zhenqiang Gong and Chaowei Xiao},
booktitle={The Fourteenth International Conference on Learning Representations},
year={2026},
url={https://openreview.net/forum?id=LfdFnakqGJ}
}